2023.11.15
Remote Security Assessment of Critical Social Infrastructure

- Kazutaka Matsuzaki
- Associate Professor, Faculty of Global Informatics, Chuo University
Areas of Specialization: Software Engineering and Control Systems Security
In recent years, the evolution of technology has connected all kinds of devices to networks, thereby enabling remote communication, control, and analysis. In this article, I will introduce research on remote assessment for the security of critical social infrastructure. In particular, from the perspective of the need for remote assessment, I will discuss the increase in cyberattacks, responses to a declining population, superiority of attacks, and the evolution of AI.
What is a security assessment of critical social infrastructure?
During assessment, test data is sent over the network to the device that serves as the controller of the system, and the reaction is monitored. The reaction will vary depending on the device.
For example, it may be easy to imagine a system such as a remote health checkup. The device that is connected to the network corresponds to the examinee in the health checkup. We ask various questions over the network and check the responses.
Particular examples of devices are those managed over a network, such as solar and wind power generation, which are representative forms of renewable energy. In addition to functioning as a virtual power plant by bundling multiple power sources, these devices also receive output control for the amount of power generated when the power supply is too ample for the demand during the long holidays in May or other occasions.
Now, what is appropriate for the various questions? Since we are conducting an assessment, rather than asking questions that are typically assumed, we ask unexpected questions and questions imagining attackers. Since there are two parties in an assessment, one-way questions are inappropriate. Questions involving "What?" "When?" "Where?" "How to send?" and "How to receive a response?" are necessary, and it is required to ask questions that match the assessment target. Assessment could be seriously negative if responses are not properly handled.
Reason for remote assessment (1): Increase in targets for cyberattacks
For example, in countries other than Japan, inverters that generate renewable energy have a wide range of functions that can be controlled over a network. Such operations are obligatory in some regions, such as California and Hawaii in the United States.
From a different point of view, this means attackers have more targets. Of course, industry groups are not sitting idle. They are strengthening their defenses by launching a security certification system.[1]
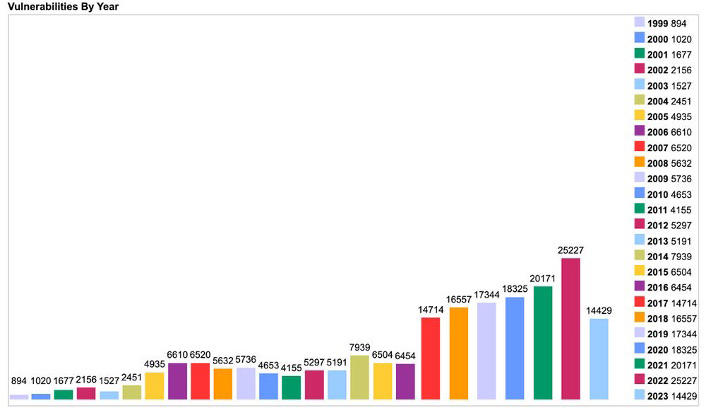
In particular, attacks increase after vulnerabilities (system weaknesses) are discovered. In 2022, more than 25,000 vulnerabilities, which is a record high, were found increased by 20% from the previous year.
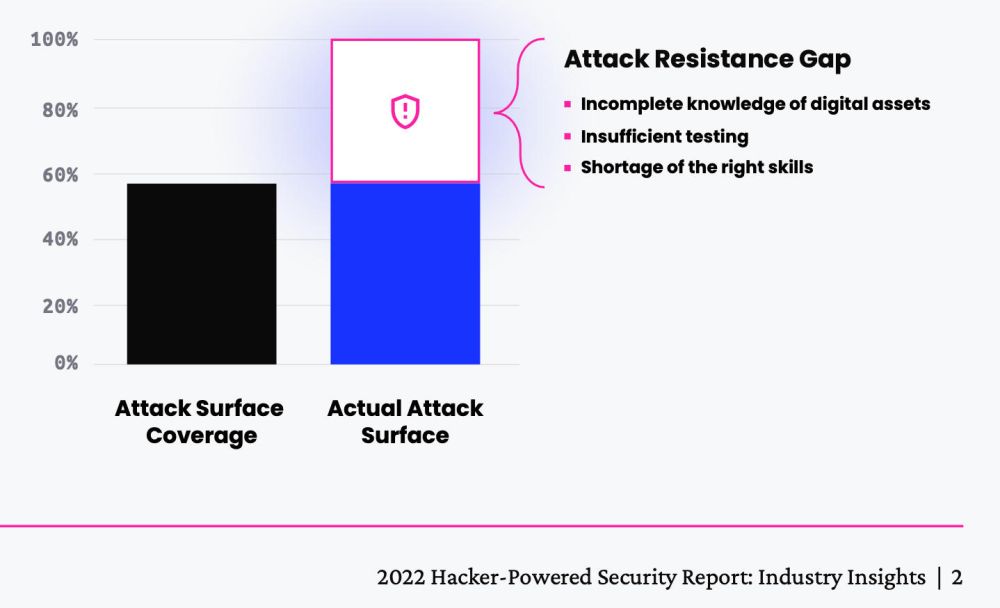
However, this is just the tip of the iceberg with a focus on commonly used software and products. A site that receives compensation for reporting bugs that lead to vulnerabilities reported 65,000 bug reports in 2022. Analysis has been attached that says configuration errors are increasing rapidly due to the effects of digital transformation (DX). Although such trends do not apply directly to social infrastructure, it cannot be said that there is no human error during system maintenance. Even if errors occur, damage can be prevented if those errors are identified immediately. This will lead to a kinder society without people being blamed for errors.[2][3]
Reason for remote assessment (2): Increased efficiency required due to decrease in working population
In response to the declining number of skilled workers and the labor population, there are many reports of cases in which drones are being used to reduce the number of people operating as part of the Smart Industrial Safety initiative promoted by the government. Inspections by drones cover a wide range of structures such as bridge piers, solar panels, power lines, and railway facilities.
The same is true for DX using generative AI as represented by ChatGPT. This can be described as an initiative to allocate labor to higher priority work.
Security is no exception when considering the labor force as a priority.
However, according to (ISC)², which is the world's largest non-profit organization of cybersecurity professional certifications, the world needs 3.4 million additional people for information security (as of 2022). Japan also needs an additional 56,000 people. My own research includes how to automatically maintain security in areas where the labor population is decreasing.[4]
Reason for remote assessment (3): Attackers have an overwhelming advantage in cyberspaces, and now AI has been added
This survey was conducted before generative AI became popular. At that time, cybercriminal organizations were suffering from burnout, while defenders were also exhausted and had a relatively high turnover rate.[5][6]
As a result, both attackers and defenders are gradually shifting their focus to security operations that rely on AI and machine learning, known as AISecOps (AI + Security + Operations).
If AISecOps proceeds smoothly, it will be an epic battle that pits offensive AI vs. defensive AI, and people will be happy and fulfilled. Will that be enough? It makes me wonder if IT and AI are truly technologies that make people's lives easier.
Conclusion: Preemptive threat detection
So far, this article has focused on the reasons for conducting remote security assessment. One of the reasons for this is AI. Although AI has existed since the 1970s, it has recently been revived and is currently showing great prosperity.
In the field of information security, there is a trend to refocus attention on technologies (symbolic execution, etc.) that have existed since the 1970s in software engineering. I believe that by incorporating these technologies into research on remote security assessment, it will be possible to make assessments that are more specific to the target of the assessment. This is enabled by the increase in the amount of advanced software released as open source, and by the ability to perform calculations that could not be done using computers of the past.
We must identify the vulnerabilities of system before attackers do, and prevent them from becoming accidentally exposed due to human error during operation and maintenance. In other words, we must recognize that there are vulnerabilities and create a mechanism to prevent them from surfacing. For that purpose, we are conducting the necessary research in collaboration with organizations such as Control System Security Center, a technology research association of Japan.
To conduct remote security assessment on a periodic basis and get rid of cyber attackers who use AI to their advantage, I hope that such cyber attackers would use their expertise for the good of the world and people.
- [1] https://sunspec.org/cybersecurity-work-group/
- [2] https://www.cve.org/About/Metrics
- [3] https://www.hackerone.com/resources/i/1487910-2022-hacker-powered-security-report-q4fy23/1?
- [4] https://www.isc2.org/-/media/2A313135414E400FA0DBD364FD74961F.ashx
- [5] https://xtech.nikkei.com/atcl/nxt/column/18/00676/062500052/
- [6] https://blogs.blackberry.com/ja/jp/2022/02/the-great-resignation-in-cybersecurity
Kazutaka Matsuzaki/Associate Professor, Faculty of Global Informatics, Chuo University Areas of Specialization: Software Engineering and Control Systems Security
Kazutaka Matsuzaki was born in 1979. He graduated from the School of Science, The University of Tokyo in 2002.
He completed the Doctoral Program in the Graduate School of Information Science and Technology, The University of Tokyo in 2007. He holds a PhD in information science and technology.
He worked at Mitsubishi Research Institute, Inc. before assuming his current position in the newly established Faculty of Global Informatics in 2019.
He serves as a chief researcher at the Tokyo Foundation for Policy Research (conducts research on the social impact of DX in Japan), and as chief investigator and expert for the domestic working group of IEC TC9, which works on PT63452/AHG20 (international standards on cybersecurity for railways).
Matsuzaki, K. and Honiden, S.
Enhancing ICS Security Diagnostics with Pseudo-Greybox Fuzzing During Maintenance Testing.
In Proceedings of the 18th International Conference on Software Technologies (ICSOFT 2023).
Matsuzaki, K., Sawada, K. and Honiden, S.
Remote Security Assessment for Cyber-Physical Systems: Adapting Design Patterns for Enhanced Diagnosis.
In Proceedings of the 20th International Conference on Security and Cryptography (SECRYPT 2023).